From 0 to pentesting hero
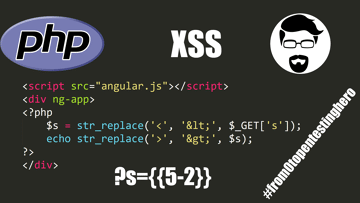
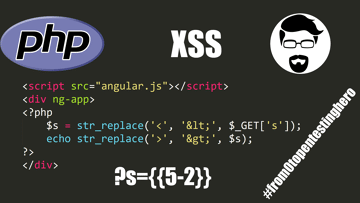
Retrieving parameters from the user and later displaying them on the website always carries risk of XSS attack. But can you perform such attack without using the HTML tag?
3 MIN READ
From 0 to pentesting hero
Retrieving parameters from the user and later displaying them on the website always carries risk of XSS attack. But can you perform such attack without using the HTML tag?
3 MIN READ
From 0 to pentesting hero
The functionality of file upload is a key place where we should pay special attention to. If the attacker successfully sends and executes a malicious file, the whole server may be taken over.
3 MIN READ
From 0 to pentesting hero
Executing system commands on the programming language level sounds like asking for trouble. But how to do it right and safe?
2 MIN READ
From 0 to pentesting hero
Every service that has a login mechanism should also have the option to reset the password. But how to do it right?
2 MIN READ
From 0 to pentesting hero
A popular opinion says to not use the pickle class on a data given by user because on deserialization it may lead to the object injection attack and malicious code execution.
2 MIN READ
From 0 to pentesting hero
We'll talk about template engines. This time we'll use Python as an example and Flask framework, in which we will use Jinja2.
2 MIN READ
From 0 to pentesting hero
Today we are going to see that the platform on which we run our programs makes a difference and we'll use PHP for this purpose.
2 MIN READ
From 0 to pentesting hero
This time, unusually - we are not going to look at a specific programming language but a Linux function - unzip - that is for extracting files.
2 MIN READ






